 When I modified the authorization content of the request through the raw tab and submitted it, the content-length should have been 140, but it became 142, causing the server to return a 500 response, although the content appeared normal. After comparing the hexview with Charles, it was indeed found that there were two extra dots. However, when I modified the authorization content of the request through the hexview tab and submitted it, the content-length was the normal 140 without any abnormal characters being automatically inserted.
When I modified the authorization content of the request through the raw tab and submitted it, the content-length should have been 140, but it became 142, causing the server to return a 500 response, although the content appeared normal. After comparing the hexview with Charles, it was indeed found that there were two extra dots. However, when I modified the authorization content of the request through the hexview tab and submitted it, the content-length was the normal 140 without any abnormal characters being automatically inserted.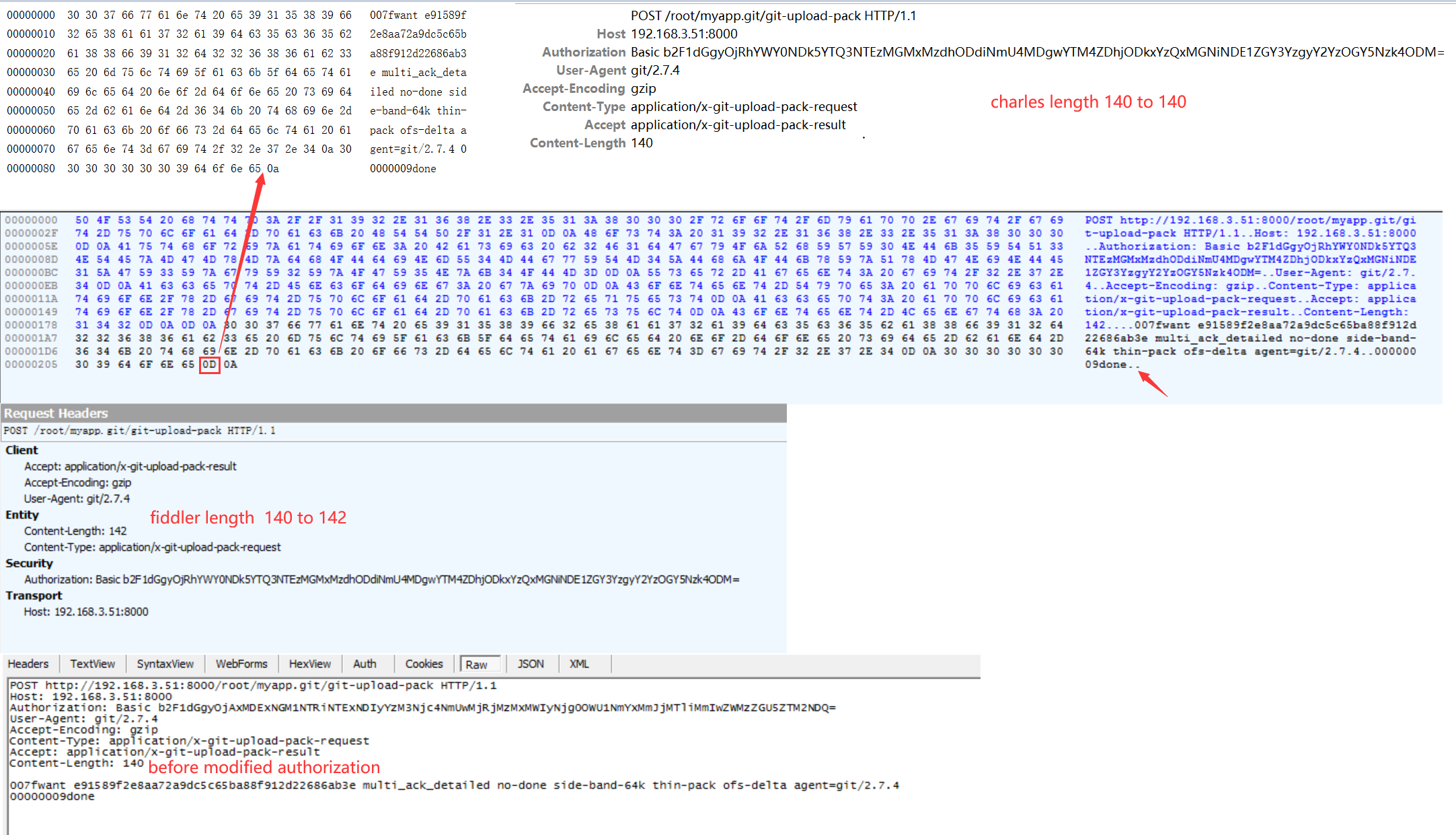
Hi, Support
When I use Fiddler Classic as a proxy in my program that uses SugarSync API, data reception fails due to sudden disconnection.
If I receive directly from the API server without going through Fiddler, there is no problem.
Whether it is a direct connection or Fiddler, the header and data of the server response are all the same.
When I look at Fiddler, all data is received, but when my program tries to get the data in the response, my Rebex Engine throws an error "Connection was closed by the remote connection end."
I also contacted Rebex, and they said that it is a close_notify error, so Fiddler does not handle it correctly.
In other words, I need to receive data after making a SugarSync API call, but the connection is disconnected without receiving a close_notify, so an error occurs when receiving data.
There is no problem in general when using Fiddler, but it only occurs when connecting to the SugarSync API server.
SugarSync API does not send Content-Length header and Content-Type header in response.
In my opinion, since there is no Content-Length or Content-Type in the header, it seems that Fiddler suddenly disconnects the client.
I hope this report will help you improve your product.
Thank you,
Best regards
BooKyung Oh
Fiddler Capture (Some data and information has been truncated and marked as ...)
Request :
POST https://api.sugarsync.com/authorization HTTP/1.1
Host: api.sugarsync.com
Content-Type: application/xml; charset=utf-8
Content-Length: 290
User-Agent: ...
Connection: keep-alive
<tokenAuthRequest>...</tokenAuthRequest>
Response :
HTTP/1.1 201 Created
Content-Type: application/xml; charset=UTF-8
Date: Sat, 14 Jun 2025 02:48:36 GMT
Location: ...
Access-Control-Allow-Origin: *
Access-Control-Allow-Headers: X-Requested-With,Content-Type,Content-Length,Authorization,Range,X-SugarSync-API-Version
Access-Control-Expose-Headers: Location,Content-Disposition,Content-Length,Accept-Ranges,Date,Transfer-Encoding,Vary
Access-Control-Max-Age: 259200
Access-Control-Allow-Methods: GET,POST,DELETE,PUT
Server: Noelios-Restlet-Engine/1.1.5
Connection: close
<?xml version="1.0" encoding="UTF-8" standalone="yes"?><authorization><expiration>2025-06-13T20:48:36.533-07:00</expiration><user>https://api.sugarsync.com/user/...</user></authorization>
Hello,
I have noticed that when rebooting from hibernation or sleep that it can happen that when the system hangs during wake-up boot and I need to hard crash it that the Windows 11 Workstation can no longer find the internet. It is only after starting Fiddler, and closing Fiddler that the Internet becomes available again.
I do not know if it is a Windows of Fiddler problem. Just wanted to pass it on.
Thanks
Dear support-reader,
I ran into an issue with the JSON-view of a request-body.
Inspector > Raw is showing alle headers and the complete body as a string, that pretty-printed looks like this:
{
"Header": {
"Name": "MyName",
"Id": 1234
},
"Item": {
"Number": 1,
"Material": "Wood"
},
"Item": {
"Number": 2,
"Material": "Gold"
},
"Item": {
"Number": 3,
"Material": "Plastic"
}
}
When switching to the JSON tab of the Inspectors-tab, the JSON-view showed, contains only the header and first Item (second and third one are missing)
Is this a bug in the Inspector JSON-view or due to the duplicate Item-keys?
Thanks for your consideration.
Regards J.
I am using the following version
Progress Telerik Fiddler Classic v5.0.20253.3311 for .NET 4.6.2
"GET ws://10.133.37.150:9999/ HTTP/1.1"
However, the URL column in the left pane says "ws://10.133.37.150:9999/", but the correct value is "/".
Also, the Inspectors' Raw tab says
"GET http://10.133.37.150:9999ws://10.133.37.150:9999/ HTTP/1.1", but the correct value is
"GET ws://10.133.37.150:9999/ HTTP/1.1".
I think this is a bug
I am using the following version
Progress Telerik Fiddler Classic v5.0.20253.3311 for .NET 4.6.2
After opening a WebSocket, the communication is captured in which the server returns the messages "WebSocket!Message1!" and "WebSocket!Message2!".With the first WebSocket, these messages are displayed in the "WebSocket" tab as expected.
However, when the exact same interaction is captured again,
these messages are not displayed in the "WebSocket" tab as they are with the second WebSocket.
Instead, they are displayed as the response body in the "Raw" tab of "Inspectors".
Whether the messages are displayed in the "WebSocket" tab or the "Raw" tab of "Inspectors" is random, and there is no visible pattern.
There seems to be a problem with the process of determining the boundary between the WebSocket opening handshake and the WebSocket message exchange.
I'm pretty disappointed in y'all.
The January 2025 version of Fiddler introduces a pointless "Security" dialog telling the user about what modules Fiddler is loading. I'm sure you thought that this would improve security, but it won't, because the same level of permission needed to add an extension to Fiddler allows the extension to make this dialog not show (base64 is not encryption).
Worse, the dialog is messed up in high-DPI to the point where it's not readable. https://bsky.app/profile/ericlawrence.com/post/3lh2wvht5oc2k
Worse, the dialog's "Always allow" button doesn't do anything when the user is using `-viewer` mode, because when in Viewer mode preferences don't work.
Worse, it looks like you also broke Transcoder extensions (File > Import); after selecting the importer to use, nothing happens.
Please go back to the way things were before. If you'd like to talk to me about Fiddler's Threat Model, I'm happy to help.
It appears that the latest version of Fiddler breaks Fiddler's public interface. The `Fiddler.WebFormats.JSON` interface no longer appears to be available, breaking extensions and scripts that depend upon it.
---------------------------
Failed to import NetLog
---------------------------
Fiddler has encountered an unexpected problem. If you believe this is a bug in Fiddler, please copy this message by hitting CTRL+C, and submit a bug report at http://www.telerik.com/forums/fiddler.
Could not load type 'JSONParseErrors' from assembly 'Fiddler, Version=5.0.20253.3311, Culture=neutral, PublicKeyToken=null'.
Type: System.TypeLoadException
Source: FiddlerImportNetlog
at FiddlerImportNetlog.NetlogImporter..ctor(StreamReader oSR, List`1 listSessions, EventHandler`1 evtProgressNotifications)
at FiddlerImportNetlog.NetLogFormatImport.ImportSessions(String sFormat, Dictionary`2 dictOptions, EventHandler`1 evtProgressNotifications)
Fiddler v5.0.20253.3311 (x64 AMD64) [.NET 4.0.30319.42000 on Microsoft Windows NT 10.0.26100.0]
---------------------------
OK
---------------------------
I am trying to use settings Tools -> Win8 Loopback Exemptions -> Exempt All -> Save Changes. But it is giving me some error and saving those changes. Following is the error.
Failed to set IsolationExempt AppContainers; call returned 0x57
I am blocked due to this error and cannot perform tests on my application. Pls help.
Thanks
Fiddler currently does not validate that the Fiddler Trusted Root Certificate is not expired when generating certificates, and it generates certificates that have an expiration that is after the expiration of the root certificate. These certificates will not work because the browser validates the expiration of each certificate in the chain.
Browsers have a poor error message for this case and will imply that the Site's certificate is expired when it's actually the ROOT that expired.
When it loads the root certificate, Fiddler should verify that it is not expired, and if it is, it should trigger the RESET ALL CERTIFICATES flow to help unblock the user from this situation.
It should also be changed such that the root certificate is valid for MUCH longer than the site certificates (e.g. 5 years for the root) so this is less likely to happen.
(If you look in the forums, users are hitting this problem and they are not sure why or how to fix it.)
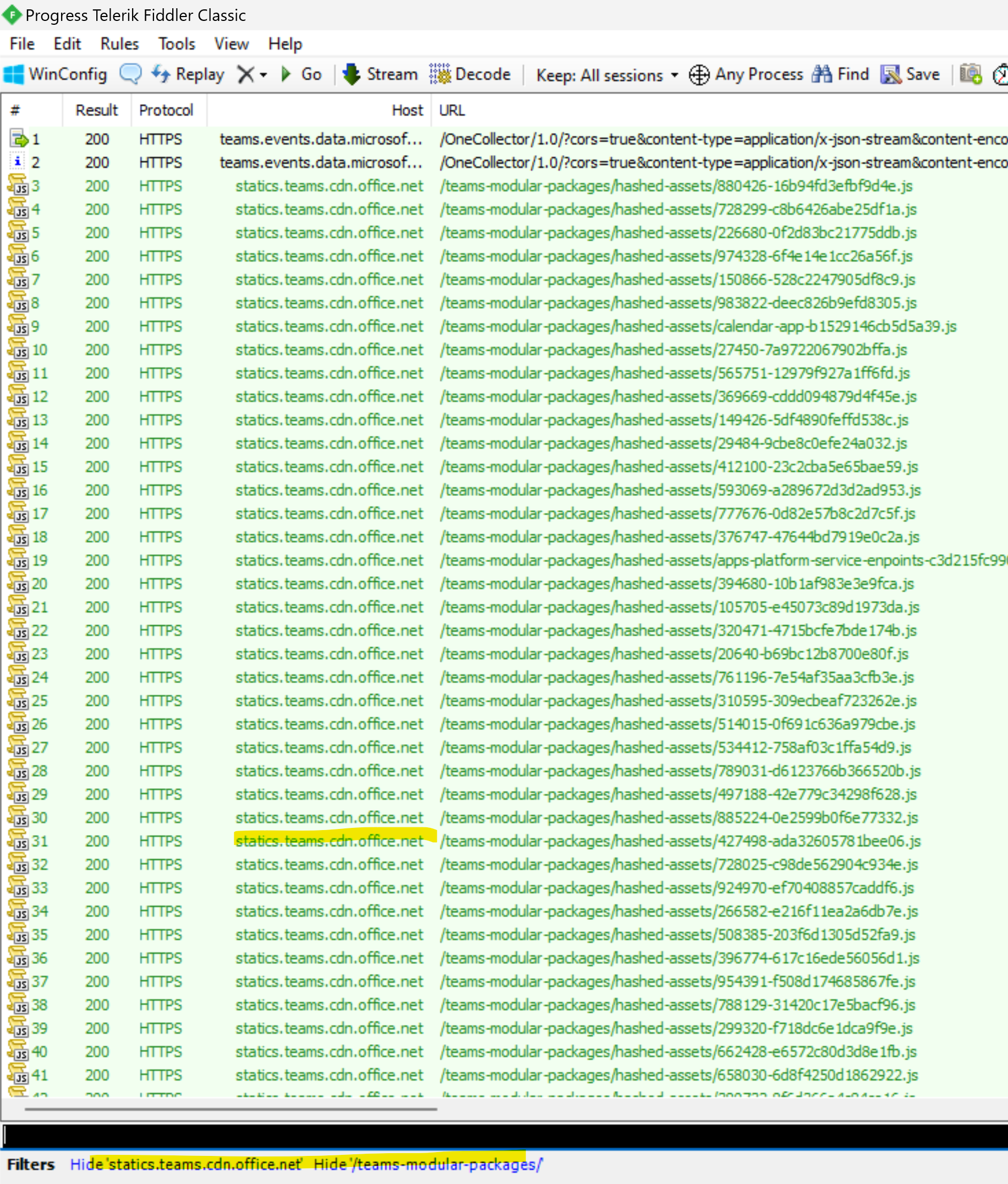
If I add a filter to hide something like /teams-modular-packages/ after closing fiddler classic and opening new file filter shows as active but is not working. I need to explicit remove filter and add it again. I would understand that filter wouldn't work accross sessions if filters were removed but they aren't and always showing in bottom left corner. This can be easily reproducible. (in this repro i have imported HAR file, not done a live capture)
Hi Team,
We wanted to use Fiddler Classic and when we send for Security Scanning, its flagged as Malicious. From your end, do you have confirmation like it would be false positive. Attached the screenshot where it was flagged as Malicious.
Thanks.
For legacy reasons, Fiddler logs the message "HTTPSLint> Warning: ClientHello record was {0} bytes long. Some servers have problems with ClientHello's greater than 255 bytes"
This message should be removed because at this point, effectively ALL clienthellos are over 500 bytes and basically all servers are okay with it.
(This message was only relevant around 2014 or so when longer clienthellos started becoming common)
When sending post data, -d option needs to ensure that the data does not start with an @
https://portswigger.net/research/the-curl-quirk-that-exposed-burp-suite-amp-google-chrome
BasicFormats.dll - cURLExport.cs
As noted in the Fiddler book,
Sessions rerouted from one hostname to another using the Host Remapping tool are rendered with a light blue
background in the Web Sessions list. HTTPS Sessions that have been rerouted have the X-IgnoreCertCNMismatch
and X-OverrideCertCN Session Flags set to avoid raising “Certificate Name Mismatch” errors.
However, there's a bug. In the HostsFile.cs code, there's are several places that look like:
if (oS.isTunnel) {
oS["x-overrideCertCN"] = oS.hostname;
oS["X-IgnoreCertCNMismatch"] = "HOSTS-Ext";
}
This usually works for browser traffic going through Fiddler (because the HTTPS handshake is typically conducted on the CONNECT tunnel). However, it doesn't work (and the user is spammed with cert error warnings) if the traffic is sent from Fiddler itself (e.g. via Composer or using the "Reissue requests" context menu item).
The code should look like this:
if (oS.isHTTPS || oS.isTunnel) {
oS["x-overrideCertCN"] = oS.hostname;
oS["X-IgnoreCertCNMismatch"] = "HOSTS-Ext";
}
Hi,
I’m developing a .NetFramework extension for Fiddler and am finding an issue with clearing bold, italic, strikethrough on the session text in the session list when using “this.session.RefreshUI()”. I’d like to be able to see these changes occur upon a context menu item click, immediately within Fiddler, without having the reload the sessions or the application. I can see the session flags are removed from the session as expected, but the bold, italic, or strikethrough is not unset.
I’m aware there is an option to Mark, Unmark sessions, but this doesn’t fit integrate closely enough with the extension I am developing or do exactly what I would like.
I seem to have no issues with changing the UI-Backcolor or UI-Color and refreshing for the updates to be immediately seen.
I can set UI-Bold, UI-Italic, UI-Strikethrough, but I cannot unset these with RefreshUI().
Is this a bug? Is the RefreshUI() call not doing something for UI-Bold, UI-Italic & UI-Strikethrough which it does do for UI-BackColor and UI-Color?
Thanks,
Jeremy.
I will be very useful if the font can be configured separately. One font for the composer and results, and the other for the IDE.
If I change the FONT, all the IDE is updated, including the composers, but after RESTARING, the composer has the same font than before
Related issue: https://github.com/aws/aws-sdk-net/issues/2567
When sending multiple requests to the same domain, sometimes Fiddler alters the headers (in this case by duplicating the user-agent one), and in this case it causes a fail because a precomputed signature of the request does not match.
good morning
i got error while capturing my app to auth.btxo.cn
=== Windows 10 64bit OS==
===Protocols I have enabled: <client>;ssl2;ssl3;tls1.0;tls1.1;tls1.2
====== Message from Fiddler v5.0.20211.51073 for .NET v4.6.1
HTTP/1.1 200 Connection Established
FiddlerGateway: Direct
Connection: close
fiddler.network.https> HTTPS handshake to 104.21.46.118 (for #17) failed. System.Security.Authentication.AuthenticationException A call to SSPI failed, see inner exception. < The message received was unexpected or badly formatted
Win32 (SChannel) Native Error Code: 0x80090326
Any help ??
Thank you
The fiddler response
A SSLv3-compatible ClientHello handshake was found. Fiddler extracted the parameters below.Version: 3.3 (TLS/1.2)
Random: 65 58 47 1D 28 AB A2 68 50 33 C7 75 1E A4 8B F5 9D A6 FB A0 F9 D2 54 FA 93 D5 AE 78 E5 26 7D 89
"Time": 26/07/1985 15:35:49
SessionID: empty
Extensions:
server_name auth.btxo.cn
status_request OCSP - Implicit Responder
supported_groups x25519 [0x1d], secp256r1 [0x17], secp384r1 [0x18]
ec_point_formats uncompressed [0x0]
signature_algs rsa_pss_rsae_sha256, rsa_pss_rsae_sha384, rsa_pss_rsae_sha512, rsa_pkcs1_sha256, rsa_pkcs1_sha384, rsa_pkcs1_sha1, ecdsa_secp256r1_sha256, ecdsa_secp384r1_sha384, ecdsa_sha1, dsa_sha1, rsa_pkcs1_sha512, ecdsa_secp521r1_sha512
SessionTicket empty
ALPN http/1.1
extended_master_secret empty
renegotiation_info 00
Ciphers:
[C02C] TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384
[C02B] TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256
[C030] TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384
[C02F] TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256
[009F] TLS_DHE_RSA_WITH_AES_256_GCM_SHA384
[009E] TLS_DHE_RSA_WITH_AES_128_GCM_SHA256
[C024] TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA384
[C023] TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256
[C028] TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384
[C027] TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256
[C00A] TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA
[C009] TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA
[C014] TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA
[C013] TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA
[009D] TLS_RSA_WITH_AES_256_GCM_SHA384
[009C] TLS_RSA_WITH_AES_128_GCM_SHA256
[003D] TLS_RSA_WITH_AES_256_CBC_SHA256
[003C] TLS_RSA_WITH_AES_128_CBC_SHA256
[0035] TLS_RSA_WITH_AES_256_CBC_SHA
[002F] TLS_RSA_WITH_AES_128_CBC_SHA
[000A] SSL_RSA_WITH_3DES_EDE_SHA
Compression:
[00] NO_COMPRESSION